=== ANCHOR POEM ===
═══════════════════════════════════════════════════════════────────────────────────
@user-1655
maybe the user could tell their client what fields to expect and how to
present them (like, a field called "memes" would be presented as a picture in
this panel, a field called "rants" would be passed to a word-cloud function
that extracts the most common 6+ letter words so you can tell at a glance what
the rant is about, this other field could be for calendar invites (plain text
of course, but interpreted by the calendar program) etc)
plus, if it's encrypted with PGP keys by default, there'd be few security
concerns. Unless your friend got hacked, or you got hacked, but, well... make
sure everything's sandboxed and don't do any remote code execution and you're
good, right?
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
=== SIMILARITY RANKED ===
--- #1 fediverse/3470 ---
════════════════════════════════════════════════════════───────────────────────────
alternatively, when you initiate an SSH session it sends you a randomized
public key whose private key is the password that you need to login. By
decrypting the string of text it sent you and sending it back (plus the
password at the end or whatever) you can ensure secure authentication without
bothering with the passwordless keys which are wayyyyyy more trouble than
they're worth and lack the "something you know" authentication method.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #2 fediverse/2674 ---
══════════════════════════════════════════════════════─────────────────────────────
┌────────────────────────────────────────────────────────────────────┐
│ CW: factually-untrue,-that-never-happened.-this-is-just-gesturing. │
└────────────────────────────────────────────────────────────────────┘
the kind of friendship where you SSH into each other's systems and leave notes
for one another.
as soon as you find one you message the person who left it like "yoooo only
just found this lol" and they're like oooo yeah did you see the bash script I
wrote in that directory "yeah totally I used it on one of my video files just
now - cool filter!"
ahhhh reminds me of all the times hackers have hacked my permanently insecure
system and left me friendly messages like "hey I'm on your side" or "how's
life, friend? I hope it's going well." or "never forget; you are worth all the
fear" y'know cute things like that
oh. right. because leaving vulnerabilities like that can lead to threat actors
affecting your stuff. how lame.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #3 fediverse/3469 ---
════════════════════════════════════════════════════════───────────────────────────
you know how SSH password login is deprecated because the password needs to be
transmitted in cleartext or whatever?
what if we just... required two passwords?
the first initiates the conversation, and sets up an encrypted line. It
doesn't matter if anyone sees the first password because they'll get a new set
of encrypted keys, meaning each session automatically is encrypted in a
different, randomized way.
the second password is the one that actually authenticates you.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #4 fediverse/4865 ---
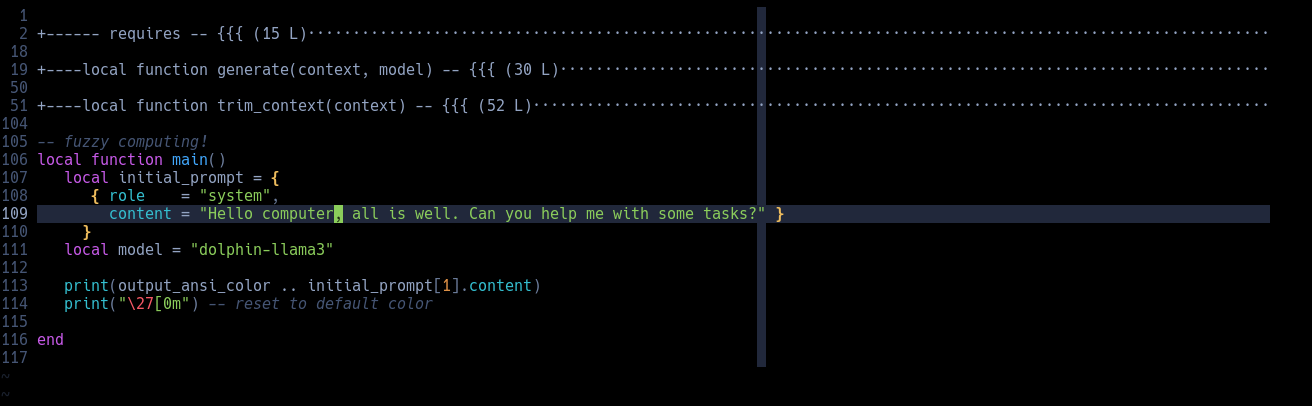
════════════════════════════════════════════════════════════════───────────────────
┌─────────────────────────┐
│ CW: computers-mentioned │
└─────────────────────────┘
this is all it takes to send a message to a local LLM.
add a third function to get chatbot functionality.
a fourth to get a database storing method
(even if it's just in .txts)
great, you've mastered the technical difficulty in using AI. Now you gotta
learn all the other kind of programming so you can use this for situations
that need interpretation moment to moment.
aka active duty systems.
something like "output a 0 if the next text is [category.iter()]: " +
output.get_content() + " \n\n output a 1 if the next text is
[category.iter()]: " + output.get_content()"
or even "describe this thing as most like one of these characteristics" until
eventually you get THX-1138 if the characters were computers.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════════════──────────────────┘
--- #5 messages/181 ---
══════════════════════════════════════════════─────────────────────────────────────
I know you don't want to hear this, but there is a chance that there will come
a time where your life depends on your ability to debug a computer without the
internet. To set up an SSH server. To install Linux. To program in C. To do
something else that I'm not prepared for... If StackOverflow didn't exist
because network connectivity has been lost, could you remember syntax? Maybe
it's a good idea to set up a local LLM that can answer basic questions about
technology. Maybe it's a good idea to set up on your parents computer, just in
case you have to hide out there for a couple months. Maybe it's a good idea to
download wikipedia, just in case.
If I need to use a mac, I'm screwed
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════────────────────────────────────────┘
--- #6 fediverse/4092 ---
═══════════════════════════════════════════════════════════────────────────────────
why not make a unified fediverse identity that can post on whatever instance
it wants?
... hmmm could be accomplished with a layer of abstraction. You could use a
"fediverse client" software to enter text into an HTML page which would have
it's own UI and stuff and would organize your accounts and instances such that
you could mark like, 3-7 as places you'd like to put a particular message.
Then it would just... do it
l m a o spam is gonna get sooooo much worse before it gets better
but trust me, we'll figure it out. And it won't be long, either. It's a
solvable problem, we just haven't built anything to handle it yet.
... yet...
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
--- #7 fediverse/3574 ---
════════════════════════════════════════════════════════───────────────────────────
@user-1564
I love the concept of this! Maybe if HTTP is too complex, you could try
another simpler server? I don't know the complexity of the programs I use
every day, but I'm sure there's one that's very simple. Even just a simple IRC
style chat server that just... sends text from person A to person B depending
on their username (like a glorified Router or Switch)
Reminded of this video tbh...:
https://www.youtube.com/watch?v=gGfTjKwLQxY
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #8 fediverse/617 ---
═════════════════════════════════════════════──────────────────────────────────────
So much of computing is just... handling the quirks of hardware and presenting
it to the user (programmer) in a way that is sane and makes sense, instead of
the arcane and [nebulous/confabulous/incomprehensible] way that physical
nature demands our absurdly potentialized computational endeavors be.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════─────────────────────────────────────┘
--- #9 fediverse/581 ---
═════════════════════════════════════════════──────────────────────────────────────
@user-428
sometimes I think about how much more productive I'd be if I had a code editor
that let me draw arrows and smiley faces and such alongside the code. Or if I
could position things strangely, like two functions side-by-side with boxes
drawn around them. Or diagrams or flowcharts or graphs or...
something that would output to raw txt format, but would present itself as an
image that could be edited.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════─────────────────────────────────────┘
--- #10 fediverse/1862 ---
╔════════════════════════════════════════════════════──────────────────────────────┐
║ some people look for signals or signs before doing something. Try and have │
║ someone in your life who can give you signals or signs so that you know when │
║ to do things. And ideally, if they're more hardcore than you, you'll know what │
║ to do, not just when to do it. │
║ │
║ did you know that anything on the internet can be read by at least one other │
║ person besides your intended recipient? There's no way they'd let us talk │
║ amongst ourselves otherwise. │
║ │
║ I think encryption is pretty neat, all you have to do is run a shell script on │
║ some text, then send that text over the internet. If you want to decrypt it, │
║ all you have to do is run a shell script on it to decrypt it. │
║ │
║ downside is, it has to be translated into plain text somewhere along the │
║ line... Maybe if we rendered the words not as text that can be read from │
║ memory, but as like, brush-strokes that can have a randomized order, but still │
║ present to the user as visual text? anyway that's what's on my mind as I try │
║ and improvise a baking recipe with yeast, flour, and butter │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧═════════════════════════════════════════───────────────────┴──────────┘
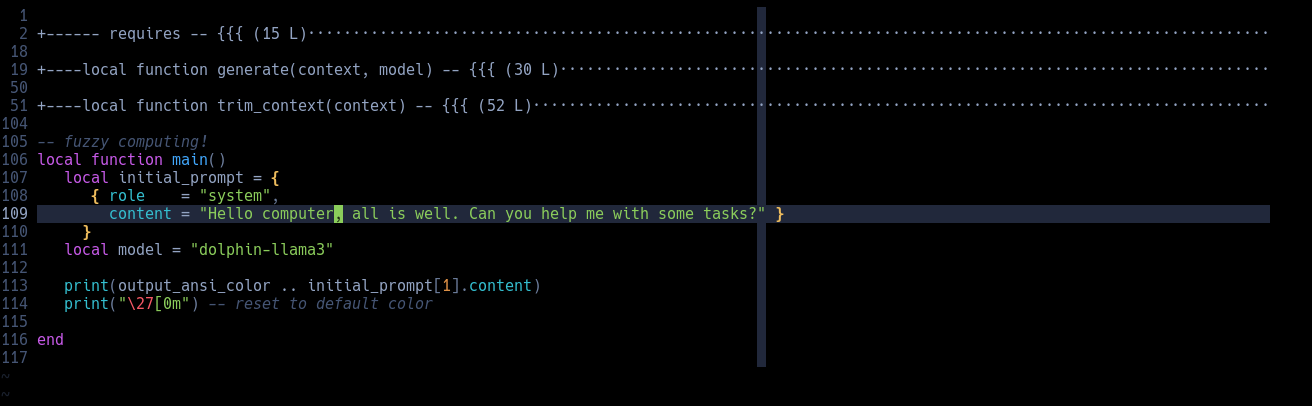
--- #11 fediverse/848 ---
══════════════════════════════════════════════─────────────────────────────────────
┌──────────────────────┐
│ CW: gentoo │
└──────────────────────┘
wrote this in an hour, used a local LLM to generate the regexes.
haven't tested it yet because I'm not on gentoo rn, so don't run it. which is
why I shared the code as an image.
if you really want the text of it then check out the visual description of the
image.
![#A script written in bash. It is used to update the Gentoo type system to the most recently written functionality. Should not be used more than once a day, and the program written here must be specifically configured to act against that functionality. However, should the user persist in their attempts to break that rule, they simply have to flip a particular switch. #!/bin/bash function gentoo-update(){ RED='\033[0;31m' NOC='\033[0m' if [ "$#" -eq 0]; then date | cat >> ~/scripts/.gentoo-update-target LAST_UPDATE_DATE="$(tail -n 1 '~/scripts/.gentoo-update-target' \ && echo "${LAST_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' THIS_UPDATE_DATE="$(date)" \ && echo "${THIS_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' if [ ${LAST_UPDATE_DATE} = ${THIS_UPDATE_DATE} ]; then printf "don't sync more than once a day! ${RED} a witch will curse you >: (${NOC}\n" else echo "syncing..." echo "${LAST_UPDATE_DATE}" | cat >> ~/scripts/.gentoo-update-target emerge --sync fi elif [ "${1}" == "-l" ]; then cat ~/scripts/.gentoo-update-target elif [ "${1}" == "-f" ]; then echo "okay but it's your funeral buddy. or worse." energe --sync fi } #A script written in bash. It is used to update the Gentoo type system to the most recently written functionality. Should not be used more than once a day, and the program written here must be specifically configured to act against that functionality. However, should the user persist in their attempts to break that rule, they simply have to flip a particular switch. #!/bin/bash function gentoo-update(){ RED='\033[0;31m' NOC='\033[0m' if [ "$#" -eq 0]; then date | cat >> ~/scripts/.gentoo-update-target LAST_UPDATE_DATE="$(tail -n 1 '~/scripts/.gentoo-update-target' \ && echo "${LAST_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' THIS_UPDATE_DATE="$(date)" \ && echo "${THIS_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' if [ ${LAST_UPDATE_DATE} = ${THIS_UPDATE_DATE} ]; then printf "don't sync more than once a day! ${RED} a witch will curse you >: (${NOC}\n" else echo "syncing..." echo "${LAST_UPDATE_DATE}" | cat >> ~/scripts/.gentoo-update-target emerge --sync fi elif [ "${1}" == "-l" ]; then cat ~/scripts/.gentoo-update-target elif [ "${1}" == "-f" ]; then echo "okay but it's your funeral buddy. or worse." energe --sync fi }](/similar-different/media/a1640a320af86532.png)
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════────────────────────────────────────┘
--- #12 fediverse/894 ---
═══════════════════════════════════════════════────────────────────────────────────
a code editor that only highlights the lines that have been specifically
flagged to have a certain function. Like, rendering, or sound, or GUI, or data
storage, or logic, or control flow.
then, when the user is browsing, they can say "only show me these types of
functions" with a very advanced filter mechanism. The editor would highlight
the ones that were relevant and related, as according to user-defined flags
that were set when writing it originally. In this way, by using a bit more
syntax, even if it's literally just blocks of [category] labels (like how """
or ``` often starts or ends a comment block)
highlighting with colors is great, but what if we de-emphasized the stuff that
didn't matter? by increasing the opacity more closely aligning the font color
to the background color, we could make a bit of text seem to "fade" from
perspective, while still readable the user's eyes would not be drawn to it.
Then, according to the labels marked as filtered, certain text would be bold,
highlighted, o
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════───────────────────────────────────┘
--- #13 messages/755 ---
═════════════════════════════════════════════════════════════════──────────────────
Code editor that moves boxes by saving over the file with a lua script every
time you moved a function call around.
Oh lemme start at the beginning:
A code editor program that's like a text editor like Vim or Emacs. If you
don't know what those are, you should probably learn Emacs. Or Vim. Up to you.
Oh right so if you do know what those mean, here's the idea: the white space
matters. It's counted and tracked into variables in a LUA script which
interface with the Vim C keybindings.
"run a function within a c program or LUA script which calls a bash command
which opens Vim for example with a file you want to edit. Then, inside the
file, your spaces and tabs would WYSIWYG for the various food ads placed
about, and then you could very easily create game design knowledge.
WASD to move, alternatively hjkl
It would run a check every time the file updates and depending on how it
changed it'd mark certain variables which would change the website as the user
moved things around.
It's just files. And files are just bits. But files are a useful abstraction,
If you realize that "ugly hacking" should be industry standard.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════════─────────────────┘
--- #14 fediverse/466 ---
═════════════════════════════════════════════──────────────────────────────────────
I love Linux. All I have to do is type "authserver" and "worldserver" and
wouldn't you know it suddenly a universe is created (with very constrained
rules) that anyone might inhabit should they desire to. It's not like I'm
perfect - oh wait I have a toot about that, gimme a sec
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════─────────────────────────────────────┘
--- #15 fediverse/1977 ---
═════════════════════════════════════════════════════──────────────────────────────
functions should be forced to describe the context of why they were being
called. I think it would help debug a lot if we supplied a reasoning for each
and every request [function call] that we made. We might even be able to parse
them into semantic pyramids which we could sorta use to estimate [tree-like
scanning] how and why the program did do wrong.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════─────────────────────────────┘
--- #16 messages/752 ---
═════════════════════════════════════════════════════════════════──────────────────
techbros really wanted to automate IRC so they didn't have to rely on the
community knowing and trusting them to remember the commands to make docker
containers for their react frameworks
and like... yeah I use chatGPT too, because that way I can get what I need
without bothering anyone (you aren't bothering people who get off on helping
others when you ask for help)
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════════─────────────────┘
--- #17 fediverse/2879 ---
══════════════════════════════════════════════════════─────────────────────────────
┌────────────────────────┐
│ CW: re: tech info-dump │
└────────────────────────┘
@user-1370
I love this a lot! I want to put function pointers in a "matrix architecture
array" and make them point to different functions at different points in the
program. I bet you could even point them at each other, so like if M and Y
then point at N, A, Y or something.
this is really cool I like stuff like this tomorrow I'll take pictures of
something similar I'm working on! I abandoned it tho hehe anyway remind me if
I forget!!
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #18 fediverse/4596 ---
═════════════════════════════════════════════════════════════──────────────────────
@user-1707
hey, I'm working on a project. Might need some python, I tend to prefer Lua
but it's pretty similar. It uses fediverse software and cheap hardware, think
raspberry pi's except risc-v
also it might use distributed local LLMs not to generate text, that's garbo
and lame and stupid. Instead it uses them to transform text, maybe even
translate text, into a more summarized form. Intentionally losing data, like a
jpeg compression but for text.
Might need some python for that. To glue it all together. The "distributed"
part is a whitelist, so we'd need to write that too. Various small little
utilities like that for connectivity.
oh also there's a one-way ethernet cable that connects two of the boards so
we'd need to store some information (easy) and send some UDP packets (hard)
anyway it's pretty neat, lmk if you want my contact details and I can tell you
about it. I might even be able to pay you.
(everything open source, no telemetry, no backdoors, everything private is
encrypted, etc etc)
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════─────────────────────┘
--- #19 fediverse/1976 ---
╔════════════════════════════════════════════════════──────────────────────────────┐
║ when pushing ctrl+v, the operating system first checks the file-type of the │
║ content being submitted. │
║ │
║ if it's like, a .jpg or .png, it knows that it's an image file. Do note that │
║ these are RANDOM letters that mean nothing, not something informative like │
║ .pic. │
║ │
║ if, however, it is text-based information, it first reads what is being sent │
║ to the application which is requesting a ctrl+v. │
║ │
║ Then, upon reading said information, it decides "is this worth passing on? │
║ Should I send something else, based on the results of what I've been analyzing │
║ of the situation as it develops over time, being observed by the execution │
║ operations of the monitor, which is projected forward unto the screen? │
║ (totally forgetting that "virtual" monitors exist, meaning monitors that don't │
║ display to any physical screen, but which rather are projected into the │
║ computer's "aetherspace", an area which is purely of the mind. │
║ │
║ Alas, that other sensors might not have read from this area. That they might │
║ not observe the results of the operations pe │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧═════════════════════════════════════════───────────────────┴──────────┘
--- #20 fediverse/1246 ---
═══════════════════════════════════════════════────────────────────────────────────
@user-883
hehe if I don't understand how it works it's difficult for me to use things.
My Linux friends get so exasperated with me because I'm like "cool script
gimme like 2 days to figure it out" and they're like "bro just use these
flags" and I'm like "no"
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════───────────────────────────────────┘
|
![#A script written in bash. It is used to update the Gentoo type system to the most recently written functionality. Should not be used more than once a day, and the program written here must be specifically configured to act against that functionality. However, should the user persist in their attempts to break that rule, they simply have to flip a particular switch. #!/bin/bash function gentoo-update(){ RED='\033[0;31m' NOC='\033[0m' if [ "$#" -eq 0]; then date | cat >> ~/scripts/.gentoo-update-target LAST_UPDATE_DATE="$(tail -n 1 '~/scripts/.gentoo-update-target' \ && echo "${LAST_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' THIS_UPDATE_DATE="$(date)" \ && echo "${THIS_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' if [ ${LAST_UPDATE_DATE} = ${THIS_UPDATE_DATE} ]; then printf "don't sync more than once a day! ${RED} a witch will curse you >: (${NOC}\n" else echo "syncing..." echo "${LAST_UPDATE_DATE}" | cat >> ~/scripts/.gentoo-update-target emerge --sync fi elif [ "${1}" == "-l" ]; then cat ~/scripts/.gentoo-update-target elif [ "${1}" == "-f" ]; then echo "okay but it's your funeral buddy. or worse." energe --sync fi } #A script written in bash. It is used to update the Gentoo type system to the most recently written functionality. Should not be used more than once a day, and the program written here must be specifically configured to act against that functionality. However, should the user persist in their attempts to break that rule, they simply have to flip a particular switch. #!/bin/bash function gentoo-update(){ RED='\033[0;31m' NOC='\033[0m' if [ "$#" -eq 0]; then date | cat >> ~/scripts/.gentoo-update-target LAST_UPDATE_DATE="$(tail -n 1 '~/scripts/.gentoo-update-target' \ && echo "${LAST_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' THIS_UPDATE_DATE="$(date)" \ && echo "${THIS_UPDATE_DATE}" \ | sed -r 's/\b(\d{4}-\d{2}-\d{2})\b/\1/g' if [ ${LAST_UPDATE_DATE} = ${THIS_UPDATE_DATE} ]; then printf "don't sync more than once a day! ${RED} a witch will curse you >: (${NOC}\n" else echo "syncing..." echo "${LAST_UPDATE_DATE}" | cat >> ~/scripts/.gentoo-update-target emerge --sync fi elif [ "${1}" == "-l" ]; then cat ~/scripts/.gentoo-update-target elif [ "${1}" == "-f" ]; then echo "okay but it's your funeral buddy. or worse." energe --sync fi }](/similar-different/media/a1640a320af86532.png)