=== ANCHOR POEM ===
══════════════════════════════════════════════════════─────────────────────────────
┌────────────────────────────────────────────────────────────────────┐
│ CW: factually-untrue,-that-never-happened.-this-is-just-gesturing. │
└────────────────────────────────────────────────────────────────────┘
the kind of friendship where you SSH into each other's systems and leave notes
for one another.
as soon as you find one you message the person who left it like "yoooo only
just found this lol" and they're like oooo yeah did you see the bash script I
wrote in that directory "yeah totally I used it on one of my video files just
now - cool filter!"
ahhhh reminds me of all the times hackers have hacked my permanently insecure
system and left me friendly messages like "hey I'm on your side" or "how's
life, friend? I hope it's going well." or "never forget; you are worth all the
fear" y'know cute things like that
oh. right. because leaving vulnerabilities like that can lead to threat actors
affecting your stuff. how lame.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
=== SIMILARITY RANKED ===
--- #1 fediverse/3470 ---
════════════════════════════════════════════════════════───────────────────────────
alternatively, when you initiate an SSH session it sends you a randomized
public key whose private key is the password that you need to login. By
decrypting the string of text it sent you and sending it back (plus the
password at the end or whatever) you can ensure secure authentication without
bothering with the passwordless keys which are wayyyyyy more trouble than
they're worth and lack the "something you know" authentication method.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #2 fediverse/3234 ---
╔═══════════════════════════════════════════════════════───────────────────────────┐
║ ┌────────────────────────────────────────────────────────────────┐ │
║ │ CW: ritz-is-fucking-stupid-I-guess-oh-whoops-cursing-mentioned │ │
║ └────────────────────────────────────────────────────────────────┘ │
║ │
║ │
║ my understanding is that anyone with my IP address could make my heart bleed │
║ due to a hardware vulnerability on my motherboard. Though you might have to │
║ get past my decrepit ancient linksys EA 3500 router from 2012 first. │
║ │
║ unrelated, but does anyone want my IP address? I don't have any remote │
║ backups, so if you hate me now would be a great time to show me how despised I │
║ am. Alternatively you could try searching for anything evil to ensure that I │
║ can be trusted. You're gonna find mostly video games and source-code that I │
║ didn't write though. But also all my notes in directories that are │
║ non-standard, meaning you'll have to look around a bit. I leave little notes │
║ everywhere I go, so that I can remind myself how to do things in the │
║ directories I revisit months later. It's so weird how sometimes the things I │
║ wrote stop working after a while even if I didn't update my system lmao │
║ │
║ what is it with artists and self-immolation? "I never thought I'd actually di │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧════════════════════════════════════════════────────────────┴──────────┘
--- #3 fediverse/5950 ---
══════════════════════════════════════════════════════════════════════════─────────
@user-138
wao I'm a cool kid _^
Hmmmm I googled "Network: file exists" and got this link:
https://access.redhat.com/solutions/1340713
my understanding of that is that maybe you're creating static routes, and for
some reason you're trying to create one that already exists? Maybe there's
something in your .bashrc config, if the file appears when you open a
terminal, or perhaps if it appears randomly then maybe there's a service or
something that's doing it.
Did you say it stopped when you swapped sim cards? ... on your phone? that's
bizzare... Maybe you were trying to create an ip route (whatever that is) that
was pointing to the same ip address as your phone? and when you swapped sims
it changed the ip address? If it appears again, maybe try setting static IP
addresses for both the phone and the computer in your router settings and see
if that fixes it. Though if you've ever seen the error while out and about at
like, a coffee shop or library or whatever, then that wouldn't apply since the
router is only for home base...
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════════════════════────────┘
--- #4 fediverse/3469 ---
════════════════════════════════════════════════════════───────────────────────────
you know how SSH password login is deprecated because the password needs to be
transmitted in cleartext or whatever?
what if we just... required two passwords?
the first initiates the conversation, and sets up an encrypted line. It
doesn't matter if anyone sees the first password because they'll get a new set
of encrypted keys, meaning each session automatically is encrypted in a
different, randomized way.
the second password is the one that actually authenticates you.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #5 fediverse/4596 ---
═════════════════════════════════════════════════════════════──────────────────────
@user-1707
hey, I'm working on a project. Might need some python, I tend to prefer Lua
but it's pretty similar. It uses fediverse software and cheap hardware, think
raspberry pi's except risc-v
also it might use distributed local LLMs not to generate text, that's garbo
and lame and stupid. Instead it uses them to transform text, maybe even
translate text, into a more summarized form. Intentionally losing data, like a
jpeg compression but for text.
Might need some python for that. To glue it all together. The "distributed"
part is a whitelist, so we'd need to write that too. Various small little
utilities like that for connectivity.
oh also there's a one-way ethernet cable that connects two of the boards so
we'd need to store some information (easy) and send some UDP packets (hard)
anyway it's pretty neat, lmk if you want my contact details and I can tell you
about it. I might even be able to pay you.
(everything open source, no telemetry, no backdoors, everything private is
encrypted, etc etc)
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════─────────────────────┘
--- #6 fediverse/239 ---
╔═══════════════════════════════════════════───────────────────────────────────────┐
║ if your computer gets hacked, but nothing was broken or changed... do you │
║ leave it as it is so that anonymous can see you're chill or do you wipe it │
║ because you're afraid it's the feds? │
║ │
║ ehhhh false dichotomy most people are afraid that their system will get borked │
║ or their bank account will be stolen or their email will get spam or that │
║ random icons will turn inside out and their mouse cursor will turn into a │
║ barfing unicorn or they'll finally have to figure out bitcoin to pay a ransom │
║ for their files including the only pictures they have of their niece. whoops │
║ │
║ people are afraid of technology because of what it can do to hurt them. │
║ they're afraid it'll break or stop working, and they'll have to spend time │
║ figuring it out. they like things how they are, but for some reason companies │
║ keep changing things? it's frustrating learning a new system, and every 5-10 │
║ years it feels like you have to learn a new paradigm and ugh it's just so │
║ exhausting. technology is not designed for users... or maybe users get bored. │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧════════════════════════════════────────────────────────────┴──────────┘
--- #7 fediverse/4883 ---
╔═══════════════════════════════════════════════════════════════───────────────────┐
║ what if you had several kindle-style paperwhite display screens. each │
║ connected to a raspberry pi that you used for compute tasks. │
║ │
║ each of these displays would display a .png file of exactly the same │
║ proportions as the size of the device. │
║ │
║ then, I could SSH into your computer and run one single command │
║ │
║ just one, stored on your computer, that you manually activate upon receiving a │
║ signal. │
║ │
║ like a virtual machine. do whatever you want with said signal, it's just a │
║ "thing" that tells you when to go. │
║ │
║ ... and run a function on a computer that performs a certain task. │
║ │
║ what task? oh right - I'd update the "today's news in cameron-ville" things │
║ every other day or so. It'd be just like, my status, my updates, here's what │
║ I'm thinking about, here's what I'm working on. │
║ │
║ you know, status updates. standups. │
║ │
║ boom, everyone knows what everyone's up to all of the time. │
║ │
║ like documenting your day for scientific purposes. except on a little device │
║ that you can scroll through with a touch. and you had like 5 or more 10+ 1 │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧════════════════════════════════════════════════════────────┴──────────┘
--- #8 fediverse/1038 ---
═══════════════════════════════════════════════────────────────────────────────────
┌──────────────────────┐
│ CW: re: what │
└──────────────────────┘
@user-766
ah yes but then how will my comrades come for my things know where to look? my
precious precious drives may be less safe inside of the computer case but at
least then someone I can about can find them.
or what you're saying is that a basic part of situational awareness is having
a plan for this kind of thing with the people who care about you? Ah, well,
nobody cares about me like that. Just a couple normies who want nothing but
business as usual.
wonder if I can open up my hard drives to "read only" SSH access? Or maybe
I'll just make the important files into a torrent. Or perhaps marking them as
"downloadable locations" on Soulseek? Plenty of options, all of them require
someone to care enough about your junk to want to archive it. Something
something ipfs?
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════───────────────────────────────────┘
--- #9 fediverse/4218 ---
═══════════════════════════════════════════════════════════────────────────────────
there are plenty of pieces of linux that are insecure in some way. Including
x11, if I remember correctly. It is purely convention to not abuse these
insecurities, and whenever you use someone else's binary software you trust
that they won't betray you in some way.
pre-built binaries are privacy violations and should be illegal. They are
security threats because the model they're built upon is necessarily insecure.
Computers will never be completely secure because of how they are built, and
so we should use locally compiled software and interpreted scripts.
Unless they're too long, or impossible to read. Who reads EULAs these days? At
least those are written in english.
maybe computers aren't worth it. Maybe computers will solve all our problems.
Who can say, maybe you should ask an oracle like me
though do remember that anything you hear can and will be used against you,
monkey's paw style. So maybe, like... don't? unless you're into magic or
schizophrenia or something
I wnt 2 be cute and tch cpus
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
--- #10 fediverse/1329 ---
╔═══════════════════════════════════════════════───────────────────────────────────┐
║ @user-941 │
║ │
║ well, your computer only has so many 1s and 0s that it can use at once. Like, │
║ having a trillion hands that can each hold a single grain of rice. Every │
║ character in that txt file would be like, 8 grains of rice, minimum, meaning │
║ you'd need at least 8 "hands" (or spots to put a zero or a one) for each │
║ letter! │
║ │
║ Hmmmm that's a lot of bits and bytes if everyone's writing to the same file. │
║ Maybe if we split the file up into smaller sections, then we could just read │
║ part of it at once. Then we could "scroll" through it to make sure we've read │
║ the whole thing, starting from the top and going to the bottom. │
║ │
║ ah but if everyone's SSHing into the same computer and reading it there, then │
║ that computer will have to present different parts of the file at different │
║ times to different people, as they read from the top to the bottom. Maybe we │
║ could just send them the file, so they can read it at their leisure? │
║ │
║ Yeah! And we could use tags to organize it and make it look pretty, like an │
║ HTML file except... wait hang on │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧════════════════════════════════════────────────────────────┴──────────┘
--- #11 messages/181 ---
══════════════════════════════════════════════─────────────────────────────────────
I know you don't want to hear this, but there is a chance that there will come
a time where your life depends on your ability to debug a computer without the
internet. To set up an SSH server. To install Linux. To program in C. To do
something else that I'm not prepared for... If StackOverflow didn't exist
because network connectivity has been lost, could you remember syntax? Maybe
it's a good idea to set up a local LLM that can answer basic questions about
technology. Maybe it's a good idea to set up on your parents computer, just in
case you have to hide out there for a couple months. Maybe it's a good idea to
download wikipedia, just in case.
If I need to use a mac, I'm screwed
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════────────────────────────────────────┘
--- #12 fediverse/5291 ---
═════════════════════════════════════════════════════════════════════──────────────
the most important skill I can think of for a linux software engineer is the
ability to connect multiple systems together and turn windows and macintosh
devices into Linux devices so that datacenters can be built out of whatever's
on the around.
there's this programming language I like called Chapel for distributed
computation computing which is also cool, if you're more of the programming
type.
networking security I believe often has hardware solutions, so getting the
crypto-graphy boys and the PCB girls together to work on some jams is a good
and productively useful gathering of insightful events
"but ritz computers should only be used to solve problems that people have,
not make more problems!" ah yes but have you considered that problems find
you, and the computers help you work through them
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════════════─────────────┘
--- #13 fediverse/1611 ---
╔═══════════════════════════════════════════════════───────────────────────────────┐
║ @user-1040 │
║ │
║ well, usually in the examples I shared like tumblr posts there's a username │
║ and picture shown. But tumblr users change their names, while on Mastodon (at │
║ least on my client) it shows your permanent handle underneath your regular │
║ changable name. I guess you could migrate accounts to another server if you're │
║ being harassed in one place, but still people have a way of finding you. It's │
║ weird kinda makes me wonder if they track you by ip address haha - did you │
║ know that every computer attached to a router uses the same public IP address? │
║ Then it uses either DHCP or static assigned local addresses for every computer │
║ on the network. That's pretty neat! I wonder why we don't have workstations by │
║ default include a router (and modem)? Seems like pretty important tech that │
║ should be built into the chassis instead of in a small separate unit. Like, │
║ what if you had to throw all your belongings into a van and drive to a motel │
║ somewhere to set up your workstation in a hotel because it's hot and your ac │
║ broke lol │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧════════════════════════════════════════────────────────────┴──────────┘
--- #14 fediverse/1994 ---
╔════════════════════════════════════════════════════──────────────────────────────┐
║ @user-1123 │
║ │
║ hi nice to meet you let me just transfer my unencoded public key to you so │
║ that you can sign it and verify that it's definitely the same thing I intended │
║ to send and not a malicious package that plans to execute itself to executable │
║ space and permanently hardwire your machine to continually feed data to an │
║ external site, no siree just a regular ordinary public key that was │
║ transferred over the internet, that place that basically guarantees a │
║ man-in-the-middle via it's communication processes over the lines and cables │
║ connecting ye to thee which are naturally administered and watched over by │
║ your host, AKA the isp. │
║ │
║ ... but yeah trust me bro plug in this flash drive, there's no way that a │
║ secret hacker might install a rootkit or something on my computer just because │
║ I plugged in a flash drive, once, literally just a nugget of information │
║ carried upon a little machine that you can fit in your pocket roughly the size │
║ of a thumb) drive, the kind that is useful for transmitting information by │
║ sneakermail. :) │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧═════════════════════════════════════════───────────────────┴──────────┘
--- #15 fediverse/6345 ---
═════════════════════════════════════════════════════════════════════════════──────
anytime I want to do something new on my computer, I write a bash script.
if I forgot how to do the thing, I spend time meandering about my
file-directory-system. If I don't find it, that's okay, because all I have to
do is keep looking until I stumble upon it.
kinda makes me wish I had an LLM who managed the operating system and named
files with long-and-descriptive titles while taking in as context the general
eternal prompt stored in ~/.claude.md or wherever
--> /home/ritz/programs/cloud-code/
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════════════════════─────┘
--- #16 fediverse/3907 ---
══════════════════════════════════════════════════════════─────────────────────────
kinda wanna make a linux distro that has all the capabilities of a GUI distro
and isn't so minimal (like screen recording, calculator, screenshot, wifi
manager, etc etc) but with i3 instead of a desktop.
they could literally just be symlinks (shortcuts) to scripts that are in your
/usr/bin or whatever directory
seriously it's not like there's THAT many ways to use ffmpeg, why not just
write a script for them? that's what you're going to do when you use it for
the first time, anyway, so...
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════────────────────────────┘
--- #17 fediverse/1762 ---
═════════════════════════════════════════════════════──────────────────────────────
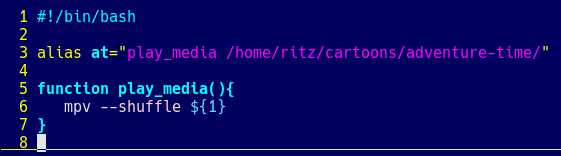
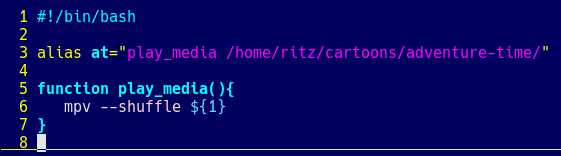
This was the first bash script I ever wrote.
It's been updated a little, it was a bash alias first, but this is what it
looks like now.
Kinda shows what kinds of problems I needed to solve most.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════─────────────────────────────┘
--- #18 fediverse/3751 ---
════════════════════════════════════════════════════════───────────────────────────
I wonder if anyone would pay me to write bash scripts for them? is there a
role that's just... bash scripter? is that what sysadmins do all day? or is
that more automation? and what the heck is a dev op? do they write bash
scripts?
or maybe writing bash scripts is the "fun" part of linux, and nobody would pay
anyone else to do it because they want to do it themselves
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #19 fediverse/1345 ---
╔═══════════════════════════════════════════════───────────────────────────────────┐
║ ┌────────────────────────────┐ │
║ │ CW: re: cursed-chromebooks │ │
║ └────────────────────────────┘ │
║ │
║ │
║ ah but are you really armed in the first place if everything you do has to be │
║ googled or stack-overflowed first │
║ │
║ are you really armed if every web page request goes through their │
║ infrastructure │
║ │
║ are you really armed if every page downloaded is directed to by their DNS │
║ │
║ perhaps it's the illusion of power that gives Linux it's attraction to nerds │
║ such as we. Perhaps we feel powerful by bash scripting a few things together │
║ and making some program that does some thing. Maybe the idea that the │
║ machinery is open and clear is what compels us to use it without fear, though │
║ as far as we can hear there's nothing about it that makes sense. │
║ │
║ I guess that's why they teach Linux in school, so that our elementary │
║ interactions with the computers that comprise our future existence will make │
║ sense to us as children. │
║ │
║ ... wait they don't do that, do they? kids get chromebooks, or didn't you │
║ hear, they're always putting boogers in the CD trays and breaking their LCD │
║ displays, much better to just start fresh │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧════════════════════════════════════────────────────────────┴──────────┘
--- #20 fediverse/5398 ---
╔═════════════════════════════════════════════════════════════════════─────────────┐
║ @user-192 │
║ │
║ step one, doesn't it suck how we have to mount drives │
║ │
║ part two, gee I sure wish networking was easier than building packets in C and │
║ pushing them over IP/TCP │
║ │
║ section three, what if every user logged in to the same system of environments │
║ and kept all their data to themselves while contributing compute to various │
║ valuable processing processes like windfall calculations and population │
║ density administrations │
║ │
║ book four, I wish I didn't have to type -p now when telling my computer │
║ goodnight, I should write a script that solves that in like 4 lines two of │
║ which are empty │
║ │
║ what about five, where they talk about sourcing functions? │
║ │
║ I like to use recursion - calling my own functions inside of my own bash │
║ scripts │
║ │
║ "something something modularity" okay docker bro like I'd really package up │
║ anything that I'm working on │
║ │
║ I mean really who really cares about how I set up the infrastructure of my │
║ system. it's gonna be unique to each person's memory of setting it up anyway, │
║ so why bother with "standardization" │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧══════════════════════════════════════════════════════════──┴──────────┘
|