=== ANCHOR POEM ===
════════════════════════════════════════════════════════───────────────────────────
┌────────────────────────────┐
│ CW: computer-toucher-stuff │
└────────────────────────────┘
"why putting SSH on a port other than 22 is a bad idea"
https://www.adayinthelifeof.nl/2012/03/12/why-putting-ssh-on-another-port-than-
22-is-bad-idea/
"When you are logged onto a system as a non-root user you cannot create a
listing TCP or UDP port below 1024. This is because port numbers below 1024
are so-called privileged ports and can only be opened by root or processes
that are running as root."
thoughts?
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
=== SIMILARITY RANKED ===
--- #1 fediverse/3469 ---
════════════════════════════════════════════════════════───────────────────────────
you know how SSH password login is deprecated because the password needs to be
transmitted in cleartext or whatever?
what if we just... required two passwords?
the first initiates the conversation, and sets up an encrypted line. It
doesn't matter if anyone sees the first password because they'll get a new set
of encrypted keys, meaning each session automatically is encrypted in a
different, randomized way.
the second password is the one that actually authenticates you.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #2 fediverse/3668 ---
════════════════════════════════════════════════════════───────────────────────────
setting up an SSH server is like a rite of passage for Linux administrators
(notice I didn't say users, you can't use linux, only administer it)
... I'm having trouble with my rites >.>
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #3 fediverse/5919 ---
══════════════════════════════════════════════════════════════════════════─────────
"but... why?"
portable linux with buttons, great for pick-up-games or communication, can
throw several in them in a backpack if you want clustered cooperation, they
work as radios (if the signal reaches) and can transmit text (if you use a
radial-style keyboard)
[this is all just a pitch for... something, what, you want something? ha
you'll find no things with me, I know nothing of antifa or whatever]
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════════════════════────────┘
--- #4 fediverse/3470 ---
════════════════════════════════════════════════════════───────────────────────────
alternatively, when you initiate an SSH session it sends you a randomized
public key whose private key is the password that you need to login. By
decrypting the string of text it sent you and sending it back (plus the
password at the end or whatever) you can ensure secure authentication without
bothering with the passwordless keys which are wayyyyyy more trouble than
they're worth and lack the "something you know" authentication method.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #5 fediverse/3631 ---
════════════════════════════════════════════════════════───────────────────────────
┌────────────────────────────────┐
│ CW: re: computer-toucher-stuff │
└────────────────────────────────┘
@user-883
I have a different port for my desktop and my laptop just in-case the router
forgets to check the postmarked address on the packets it receives... at least
it'll know which port to send it to!
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #6 messages/181 ---
══════════════════════════════════════════════─────────────────────────────────────
I know you don't want to hear this, but there is a chance that there will come
a time where your life depends on your ability to debug a computer without the
internet. To set up an SSH server. To install Linux. To program in C. To do
something else that I'm not prepared for... If StackOverflow didn't exist
because network connectivity has been lost, could you remember syntax? Maybe
it's a good idea to set up a local LLM that can answer basic questions about
technology. Maybe it's a good idea to set up on your parents computer, just in
case you have to hide out there for a couple months. Maybe it's a good idea to
download wikipedia, just in case.
If I need to use a mac, I'm screwed
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════────────────────────────────────────┘
--- #7 fediverse/874 ---
══════════════════════════════════════════════─────────────────────────────────────
oh yeah well if SSH keys are so secure then why doesn't every website on Earth
require them
really though why doesn't every website on Earth require them
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════────────────────────────────────────┘
--- #8 fediverse/466 ---
═════════════════════════════════════════════──────────────────────────────────────
I love Linux. All I have to do is type "authserver" and "worldserver" and
wouldn't you know it suddenly a universe is created (with very constrained
rules) that anyone might inhabit should they desire to. It's not like I'm
perfect - oh wait I have a toot about that, gimme a sec
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════─────────────────────────────────────┘
--- #9 fediverse/2674 ---
══════════════════════════════════════════════════════─────────────────────────────
┌────────────────────────────────────────────────────────────────────┐
│ CW: factually-untrue,-that-never-happened.-this-is-just-gesturing. │
└────────────────────────────────────────────────────────────────────┘
the kind of friendship where you SSH into each other's systems and leave notes
for one another.
as soon as you find one you message the person who left it like "yoooo only
just found this lol" and they're like oooo yeah did you see the bash script I
wrote in that directory "yeah totally I used it on one of my video files just
now - cool filter!"
ahhhh reminds me of all the times hackers have hacked my permanently insecure
system and left me friendly messages like "hey I'm on your side" or "how's
life, friend? I hope it's going well." or "never forget; you are worth all the
fear" y'know cute things like that
oh. right. because leaving vulnerabilities like that can lead to threat actors
affecting your stuff. how lame.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #10 fediverse/2622 ---
══════════════════════════════════════════════════════─────────────────────────────
what kind of linux user are you if you don't even like reading terminal
output? it's USEFUL and INTERESTING information!
WHY ELSE WOULD THE PROGRAMMER OUTPUT IT???
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #11 fediverse/1482 ---
════════════════════════════════════════════════───────────────────────────────────
@user-192
I feel like SSH keys to log into every website should be a standard
or something similar
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════──────────────────────────────────┘
--- #12 fediverse/5950 ---
══════════════════════════════════════════════════════════════════════════─────────
@user-138
wao I'm a cool kid _^
Hmmmm I googled "Network: file exists" and got this link:
https://access.redhat.com/solutions/1340713
my understanding of that is that maybe you're creating static routes, and for
some reason you're trying to create one that already exists? Maybe there's
something in your .bashrc config, if the file appears when you open a
terminal, or perhaps if it appears randomly then maybe there's a service or
something that's doing it.
Did you say it stopped when you swapped sim cards? ... on your phone? that's
bizzare... Maybe you were trying to create an ip route (whatever that is) that
was pointing to the same ip address as your phone? and when you swapped sims
it changed the ip address? If it appears again, maybe try setting static IP
addresses for both the phone and the computer in your router settings and see
if that fixes it. Though if you've ever seen the error while out and about at
like, a coffee shop or library or whatever, then that wouldn't apply since the
router is only for home base...
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════════════════════────────┘
--- #13 fediverse/3234 ---
╔═══════════════════════════════════════════════════════───────────────────────────┐
║ ┌────────────────────────────────────────────────────────────────┐ │
║ │ CW: ritz-is-fucking-stupid-I-guess-oh-whoops-cursing-mentioned │ │
║ └────────────────────────────────────────────────────────────────┘ │
║ │
║ │
║ my understanding is that anyone with my IP address could make my heart bleed │
║ due to a hardware vulnerability on my motherboard. Though you might have to │
║ get past my decrepit ancient linksys EA 3500 router from 2012 first. │
║ │
║ unrelated, but does anyone want my IP address? I don't have any remote │
║ backups, so if you hate me now would be a great time to show me how despised I │
║ am. Alternatively you could try searching for anything evil to ensure that I │
║ can be trusted. You're gonna find mostly video games and source-code that I │
║ didn't write though. But also all my notes in directories that are │
║ non-standard, meaning you'll have to look around a bit. I leave little notes │
║ everywhere I go, so that I can remind myself how to do things in the │
║ directories I revisit months later. It's so weird how sometimes the things I │
║ wrote stop working after a while even if I didn't update my system lmao │
║ │
║ what is it with artists and self-immolation? "I never thought I'd actually di │
╟─────────┐ ┌───────────┤
║ similar │ chronological │ different │
╚═════════╧════════════════════════════════════════════────────────────┴──────────┘
--- #14 fediverse/5977 ---
══════════════════════════════════════════════════════════════════════════─────────
apparently you can use network sockets for inter-process communication if you
just set the network to your home and the ports that are set to the defaults
that people who know what software you use will know to listen on when they've
hacked any single device on your network. good thing that data is with the
router, right?
what if there was a stop before leaving the computer?
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════════════════════────────┘
--- #15 messages/1245 ---
═════════════════════════════════════════════════════════════════════════════════──
BRB, if you want to talk to yourselfs, I recommend opening a port in your
router and exchanging HTTP packets that create messages on each other's
computers. Can be done in a couple hundred lines of C code that can be 90%
premade or auto-generated. Then, once it's made, you don't have to think about
it again because it's so simple. It's not trying to scale, it's just...
designed for a small, focused, human oriented mindset.\
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════════════════════════─┘
--- #16 fediverse/5291 ---
═════════════════════════════════════════════════════════════════════──────────────
the most important skill I can think of for a linux software engineer is the
ability to connect multiple systems together and turn windows and macintosh
devices into Linux devices so that datacenters can be built out of whatever's
on the around.
there's this programming language I like called Chapel for distributed
computation computing which is also cool, if you're more of the programming
type.
networking security I believe often has hardware solutions, so getting the
crypto-graphy boys and the PCB girls together to work on some jams is a good
and productively useful gathering of insightful events
"but ritz computers should only be used to solve problems that people have,
not make more problems!" ah yes but have you considered that problems find
you, and the computers help you work through them
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════════════─────────────┘
--- #17 fediverse/6061 ---
═══════════════════════════════════════════════════════════════════════════────────
what if (hear me out)
what if instead of TCP we just did a constant stream of UDP packets until the
recipient said "OKAY OKAY I GET IT"
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════════════════════───────┘
--- #18 fediverse/1310 ---
════════════════════════════════════════════════───────────────────────────────────
that feeling when you type your password so fast that one hand is faster than
the other and the letters get all jumbled and now you have to remake your ssh
key -.-
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════──────────────────────────────────┘
--- #19 fediverse/1693 ---
════════════════════════════════════════════════════───────────────────────────────
"if I work on the TTY then they can't forward my X session without my consent"
- ramblings of the utterly deranged
as if they couldn't just look at your unencrypted source-code as you save it
to your hard drive smh
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════──────────────────────────────┘
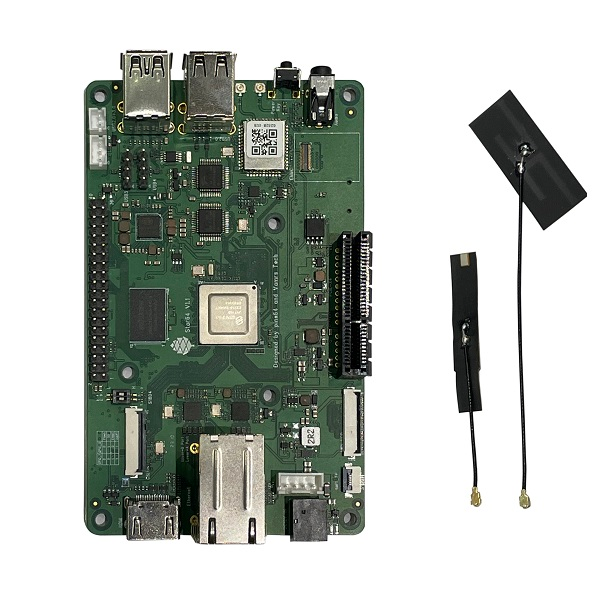
--- #20 fediverse/6126 ---
═══════════════════════════════════════════════════════════════════════════────────
@user-1900
if you can do ethernet instead of usb, this might work:
https://pine64.com/product/star64-model-a-8gb-single-board-computer/
it's got two ethernet ports.

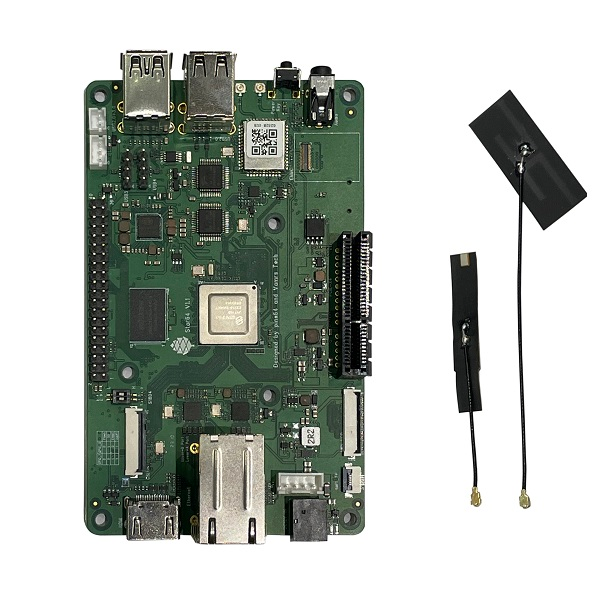


┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════════════════════───────┘
|