=== ANCHOR POEM ===
════════════════════════════════════════════════════════───────────────────────────
@user-579
I think I remember reading once that you can opt-in to encryption with
Telegram? But it's kinda pointless unless both parties do so. My understanding
is that everyone should be using Signal, or if you're really paranoid use PGP
encryption
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
=== SIMILARITY RANKED ===
--- #1 fediverse/4930 ---
════════════════════════════════════════════════════════════════───────────────────
hi does anyone know of an app that non tech people could use that's like
"signal but organized like discord" with channels and threads and such?
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════════════──────────────────┘
--- #2 fediverse/4194 ---
═══════════════════════════════════════════════════════════────────────────────────
I guess I'm used to messaging applications where it's expected that you'll
send what you're typing after every complete thought
giving people space to return their own completed trains of... "thought" but
without saying "thought" again because I just said it at the end of the
previous... sentence? paragraph? idk anymore it feels weird to post like this
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
--- #3 fediverse/5913 ---
══════════════════════════════════════════════════════════════════════════─────────
Did you know that any wifi chip can be used as both a sender and a receiver?
how do you think you'd get data in and out of the device?
trick is... you don't actually need a router. How fun is that!
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════════════════════────────┘
--- #4 fediverse/1693 ---
════════════════════════════════════════════════════───────────────────────────────
"if I work on the TTY then they can't forward my X session without my consent"
- ramblings of the utterly deranged
as if they couldn't just look at your unencrypted source-code as you save it
to your hard drive smh
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════──────────────────────────────┘
--- #5 fediverse/1254 ---
═══════════════════════════════════════════════────────────────────────────────────
@user-889
I'm always here if you need me. Let me know if you'd prefer Telegram or
something.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════───────────────────────────────────┘
--- #6 fediverse/5369 ---
══════════════════════════════════════════════════════════════════════─────────────
@user-138
you can use a username now. They added that functionality recently.
it's supposedly more encrypted or something. But, it's still a centralized
point of failure. If you want to say something privately, pretend like you're
ordering drugs on the dark web and use PGP encryption or SSH keys or whatever
it says in the "how to order drugs on the dark web" guides.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════════════════────────────┘
--- #7 messages/635 ---
════════════════════════════════════════════════════════════───────────────────────
Yeah, sure, signal is encrypted, but they could just put a virus on your
miniature pocket tv that streams your screen into a text recognition bot which
streams that text into an LLM trained to report on suspicious seditious
activity.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════════──────────────────────┘
--- #8 fediverse/4172 ---
═══════════════════════════════════════════════════════════────────────────────────
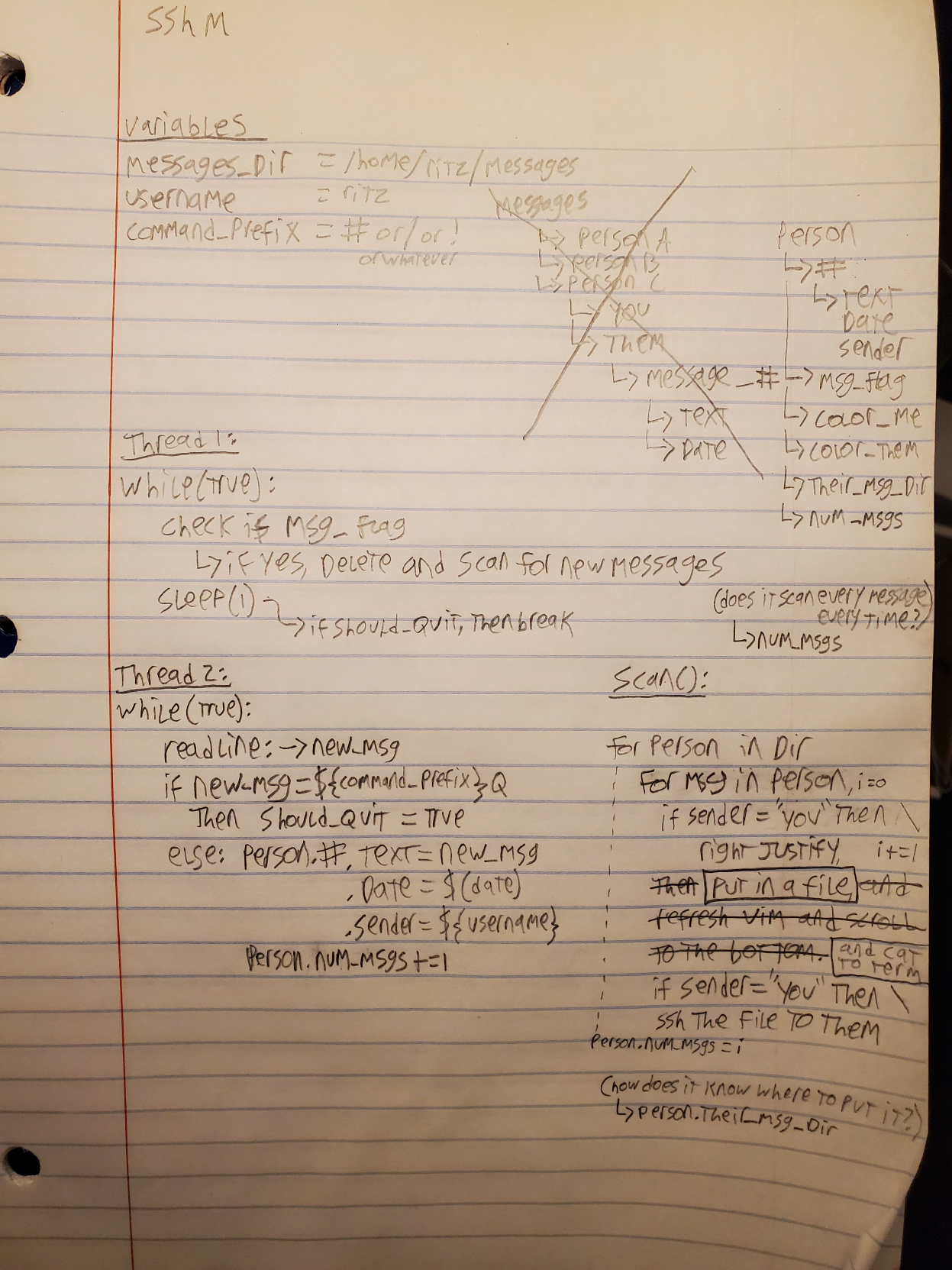
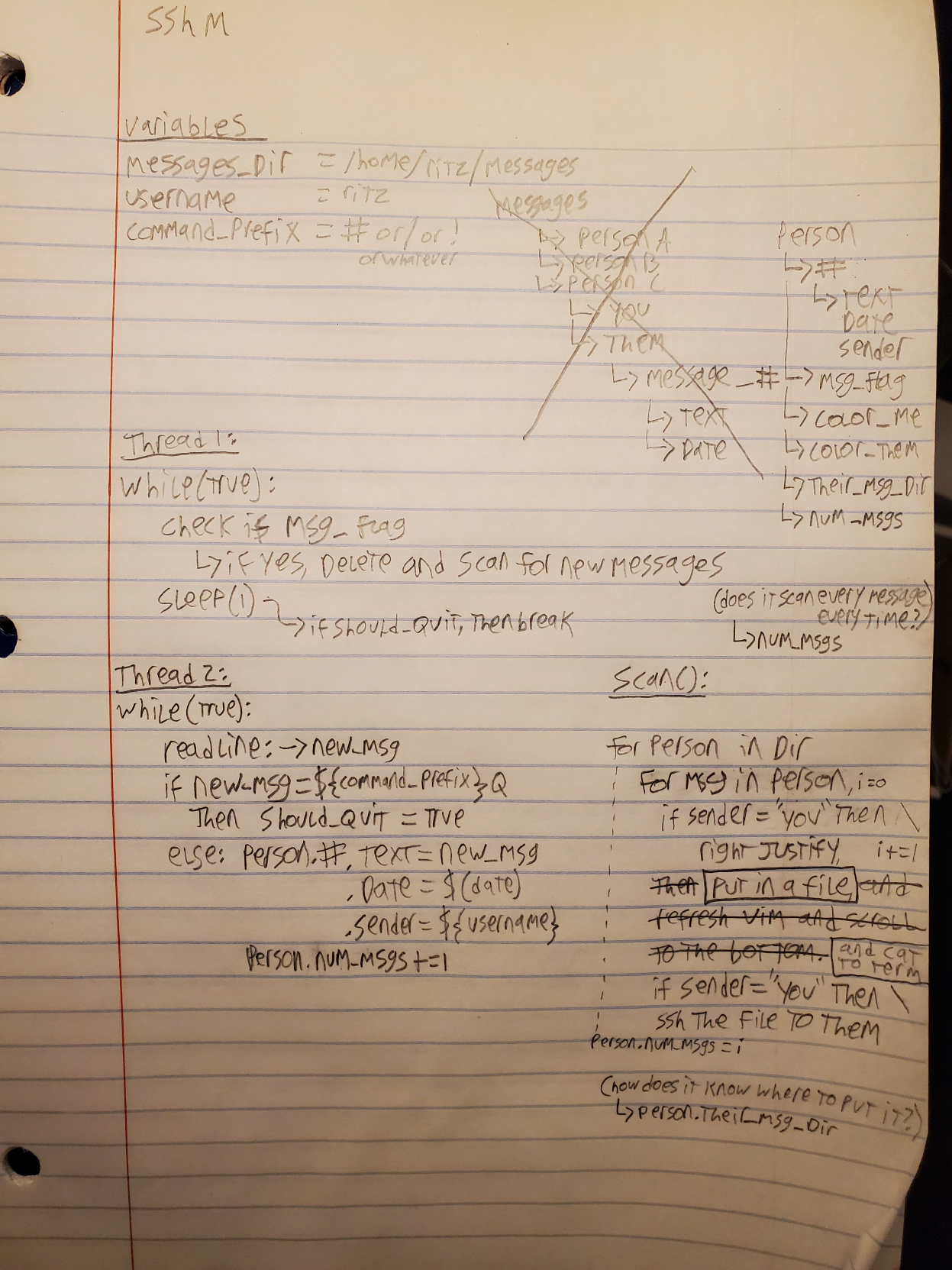
this is what I got so far for a messaging client that uses SSH
... so you need someone's public key in order to talk to them
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
--- #9 fediverse/624 ---
═════════════════════════════════════════════──────────────────────────────────────
You know, there's no guarantee that Youtube or Gmail has to show you the EXACT
SAME video or message that your friend shared with you. Or did they even share
it at all? So hard to tell when they know all the communication you've ever
had, because you only know each other online on their platforms, [read: US
government observed platforms] [like, HTTPS] surely there's no room for
someone to sneak in and edit your conversations. Surely the only way to
securely communicate is to send pure PGP encrypted bytes to another target,
wrapped in a TCP/IP header, with unknown intent or expression. Worst they
could do then is just, y'know, block it entirely.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════─────────────────────────────────────┘
--- #10 fediverse/2281 ---
══════════════════════════════════════════════════════─────────────────────────────
I'd be a terrible spy. Not only is my opsec something that someone needs to
teach me, I'm much too busy to implement things without their help. I am
unabashedly compassionate though, so just ask and I'll pour love from my heart.
But hey! There's always time to practice, each moment you can think "what kind
of a sign is this?"
Like a crazy person following the will of god, or a nature witch listening to
the wind in the trees.
What they often get wrong, and what they could be better at hearing, is that
signals are not signs unless they're out of the ordinary.
Trick is, if you're a spy, then you need to leave signals that are visible
enough to your quarry, but not to the stars.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #11 fediverse/3454 ---
════════════════════════════════════════════════════════───────────────────────────
deleting messages is pointless.
it's always better to assume that they'll be screenshotted before you post.
anything you say on the internet can and WILL be used against you
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #12 fediverse/2252 ---
══════════════════════════════════════════════════════─────────────────────────────
┌──────────────────────┐
│ CW: tech-encryption │
└──────────────────────┘
users don't want to have to think about encryption keys.
they should be available for them if they need them, in like... a folder or
something somewhere, but they don't need to really know that they exist.
more friction like that keeps people away from being secure.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #13 fediverse/6209 ---
════════════════════════════════════════════════════════════════════════════───────
okay just to clarify: if anyone is recording me or storing data about me, I
would really prefer if you didn't delete it just because I realized it was
happening. I like data! It's cool to know such things!
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════════════════════════──────┘
--- #14 messages/352 ---
═══════════════════════════════════════════════════────────────────────────────────
Though, of course, can you ever be sure who is who they say they are? You must
consider all messages anonymous by default, and unencrypted (untrustable) and
yet impossible to ignore. Like the messages they had to ignore at Bletchley
Park to avoid the suspicion that they'd figured out the secret code. You know
how it goes.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════───────────────────────────────┘
--- #15 fediverse/3366 ---
═══════════════════════════════════════════════════════────────────────────────────
I don't know who needs to hear this, but if your friend sends you a paragraph
you don't have to respond with a paragraph.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════───────────────────────────┘
--- #16 fediverse/2044 ---
═════════════════════════════════════════════════════──────────────────────────────
honestly I think everyone should have two mastodon accounts - one for people
you like, and one for people you trust
(I have one)
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════─────────────────────────────┘
--- #17 fediverse/4356 ---
═══════════════════════════════════════════════════════════────────────────────────
┌──────────────────────────────────────────────────────────────────────────────┐
│ CW: don't-even-get-me-started-on-people-who-don't-lock-their-phone-with-at-least-a-pin │
└──────────────────────────────────────────────────────────────────────────────┘
if they can't get into your phone, they can at least record all of the
received notifications.
meaning they already know who it is that you know...
without having to find people that are distant or unrelated
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
--- #18 fediverse/1293 ---
════════════════════════════════════════════════───────────────────────────────────
┌──────────────────────────────────────────────────────────────────────────────┐
│ CW: re: fedi meta, the bad space, fediblock, misleading and untrue cw, uspol, speedrunning discourse, industrial revolution, aquarium tips │
└──────────────────────────────────────────────────────────────────────────────┘
@user-921
where tf is all this discourse I always hear about like what are ya'll talking
about
... are you talking about me
[silly intrusive thoughts teehee pay no mind]
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════──────────────────────────────────┘
--- #19 fediverse/3313 ---
═══════════════════════════════════════════════════════────────────────────────────
what if it was illegal to add network connectivity to a device that the user
didn't explicitly request to have network connectivity?
I'm picturing any device being sold going forward to have a little radio
button with like "add network features (+10$)" and "no networking included
(+0$)"
boom, no more IoT
no more dishwashers phoning home telemetry
no more consensual privacy invasions desecrations
no more "I thought it was just a polaroid camera why does it have bluetooth
enabled without broadcasting a pairing request?"
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════───────────────────────────┘
--- #20 messages/701 ---
══════════════════════════════════════════════════════════════─────────────────────
one sec gotta send something else from my phone... now, what was it, hmmmmm
lemme think
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════════════────────────────────┘
|