=== ANCHOR POEM ===
════════════════════════════════════════════════════════───────────────────────────
@user-883
it might be, I don't know much about it (hence why I'm asking questions) but I
have heard that ssh keys are more secure than password authentication and it
never made sense to me. If availability is important for security purposes,
then wouldn't SSH keys (which are much more difficult to carry around than a
password) be less suitable?
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
=== SIMILARITY RANKED ===
--- #1 fediverse/1310 ---
════════════════════════════════════════════════───────────────────────────────────
that feeling when you type your password so fast that one hand is faster than
the other and the letters get all jumbled and now you have to remake your ssh
key -.-
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════──────────────────────────────────┘
--- #2 fediverse/3470 ---
════════════════════════════════════════════════════════───────────────────────────
alternatively, when you initiate an SSH session it sends you a randomized
public key whose private key is the password that you need to login. By
decrypting the string of text it sent you and sending it back (plus the
password at the end or whatever) you can ensure secure authentication without
bothering with the passwordless keys which are wayyyyyy more trouble than
they're worth and lack the "something you know" authentication method.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #3 fediverse/874 ---
══════════════════════════════════════════════─────────────────────────────────────
oh yeah well if SSH keys are so secure then why doesn't every website on Earth
require them
really though why doesn't every website on Earth require them
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════────────────────────────────────────┘
--- #4 fediverse/3469 ---
════════════════════════════════════════════════════════───────────────────────────
you know how SSH password login is deprecated because the password needs to be
transmitted in cleartext or whatever?
what if we just... required two passwords?
the first initiates the conversation, and sets up an encrypted line. It
doesn't matter if anyone sees the first password because they'll get a new set
of encrypted keys, meaning each session automatically is encrypted in a
different, randomized way.
the second password is the one that actually authenticates you.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #5 fediverse/2252 ---
══════════════════════════════════════════════════════─────────────────────────────
┌──────────────────────┐
│ CW: tech-encryption │
└──────────────────────┘
users don't want to have to think about encryption keys.
they should be available for them if they need them, in like... a folder or
something somewhere, but they don't need to really know that they exist.
more friction like that keeps people away from being secure.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #6 fediverse/1505 ---
═════════════════════════════════════════════════──────────────────────────────────
2 factor authentication is not for security. If they cared about security they
would use SSH keys.
2FA is so that your email provider knows whenever you log in somewhere. Most
people use gmail.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════─────────────────────────────────┘
--- #7 messages/181 ---
══════════════════════════════════════════════─────────────────────────────────────
I know you don't want to hear this, but there is a chance that there will come
a time where your life depends on your ability to debug a computer without the
internet. To set up an SSH server. To install Linux. To program in C. To do
something else that I'm not prepared for... If StackOverflow didn't exist
because network connectivity has been lost, could you remember syntax? Maybe
it's a good idea to set up a local LLM that can answer basic questions about
technology. Maybe it's a good idea to set up on your parents computer, just in
case you have to hide out there for a couple months. Maybe it's a good idea to
download wikipedia, just in case.
If I need to use a mac, I'm screwed
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════────────────────────────────────────┘
--- #8 fediverse/1693 ---
════════════════════════════════════════════════════───────────────────────────────
"if I work on the TTY then they can't forward my X session without my consent"
- ramblings of the utterly deranged
as if they couldn't just look at your unencrypted source-code as you save it
to your hard drive smh
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════──────────────────────────────┘
--- #9 fediverse/4093 ---
═══════════════════════════════════════════════════════════────────────────────────
I have no idea why people prefer a GUI when working with software. How the
heck do they expect to use their computer remotely if they can't even run
their software over SSH?
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
--- #10 fediverse/3668 ---
════════════════════════════════════════════════════════───────────────────────────
setting up an SSH server is like a rite of passage for Linux administrators
(notice I didn't say users, you can't use linux, only administer it)
... I'm having trouble with my rites >.>
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════──────────────────────────┘
--- #11 fediverse/1482 ---
════════════════════════════════════════════════───────────────────────────────────
@user-192
I feel like SSH keys to log into every website should be a standard
or something similar
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════──────────────────────────────────┘
--- #12 fediverse/4107 ---
═══════════════════════════════════════════════════════════────────────────────────
Just configured Wake on LAN so I can turn on my desktop from anywhere. As long
as I have the right SSH key...
Couldn't figure out how to do Wake on WAN, which I think is somehow more
secure. This way uses a small jump from a separate tiny computer which is
always on.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
--- #13 fediverse/2257 ---
══════════════════════════════════════════════════════─────────────────────────────
if you don't know how long you're going to be gone, how do you know what to
bring? like, is it a "grab the hard drives" kind of trip, or is it more like
"we'll return in the spring"?
who can say, depends on who's driving.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═══════════════════════════════════════════════────────────────────────────┘
--- #14 fediverse/5311 ---
═════════════════════════════════════════════════════════════════════──────────────
I don't know anything about cryptography 🙃 😋 🥴
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════════════════════─────────────┘
--- #15 fediverse/4946 ---
════════════════════════════════════════════════════════════════───────────────────
I would trust the CIA if they gave me continual access to all surveillance of
myself
-- stack overflow --
what if you made a program which cycled credentials?
like... "give me a random credential for Zoom" because we share all of our
digital resources
did you get banned for account sharing? no you didn't because you routed
through the correct VPN
automagically
[has never had a software job]
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧═════════════════════════════════════════════════════════──────────────────┘
--- #16 fediverse/4720 ---
═══════════════════════════════════════════════════════════════────────────────────
@user-882
it's a security hole though
yeah... there ya go...
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════════───────────────────┘
--- #17 fediverse/1870 ---
═════════════════════════════════════════════════════──────────────────────────────
why would I want other people using my computer? They don't know how to use my
computer! They might break something or mess something up or automatically
read/edit my files that are stored in standard locations through the usage of
a script which automagically scans and ransomwares machines on the internet
who store their files in specific standardized locations! no thank you.
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧══════════════════════════════════════════════─────────────────────────────┘
--- #18 fediverse/1246 ---
═══════════════════════════════════════════════────────────────────────────────────
@user-883
hehe if I don't understand how it works it's difficult for me to use things.
My Linux friends get so exasperated with me because I'm like "cool script
gimme like 2 days to figure it out" and they're like "bro just use these
flags" and I'm like "no"
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════───────────────────────────────────┘
--- #19 fediverse/4751 ---
═══════════════════════════════════════════════════════════════────────────────────
apparently security through obscurity is out, and security through community
is in, don't ask me how I know that teehee
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════════───────────────────┘
--- #20 fediverse/4172 ---
═══════════════════════════════════════════════════════════────────────────────────
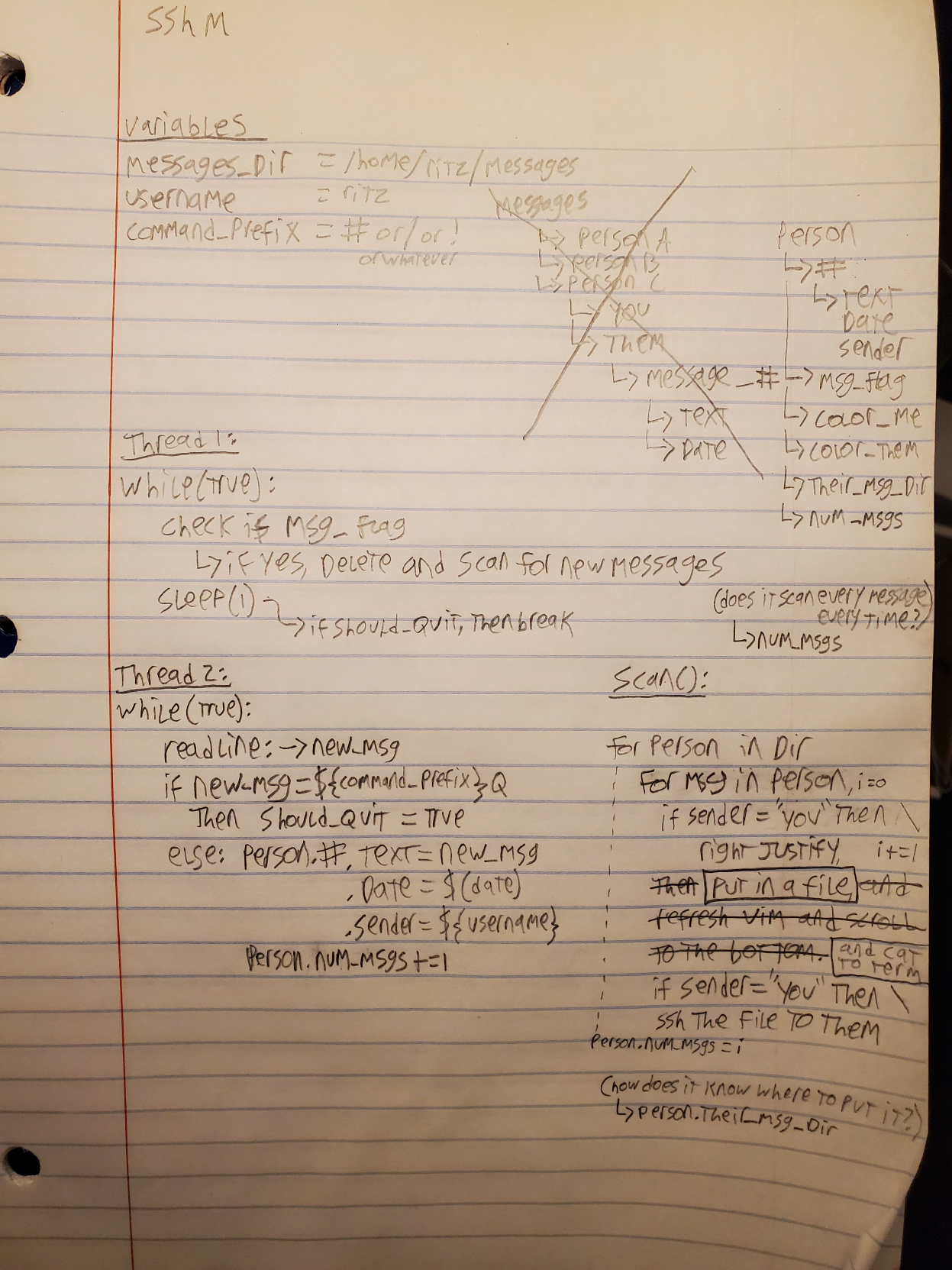
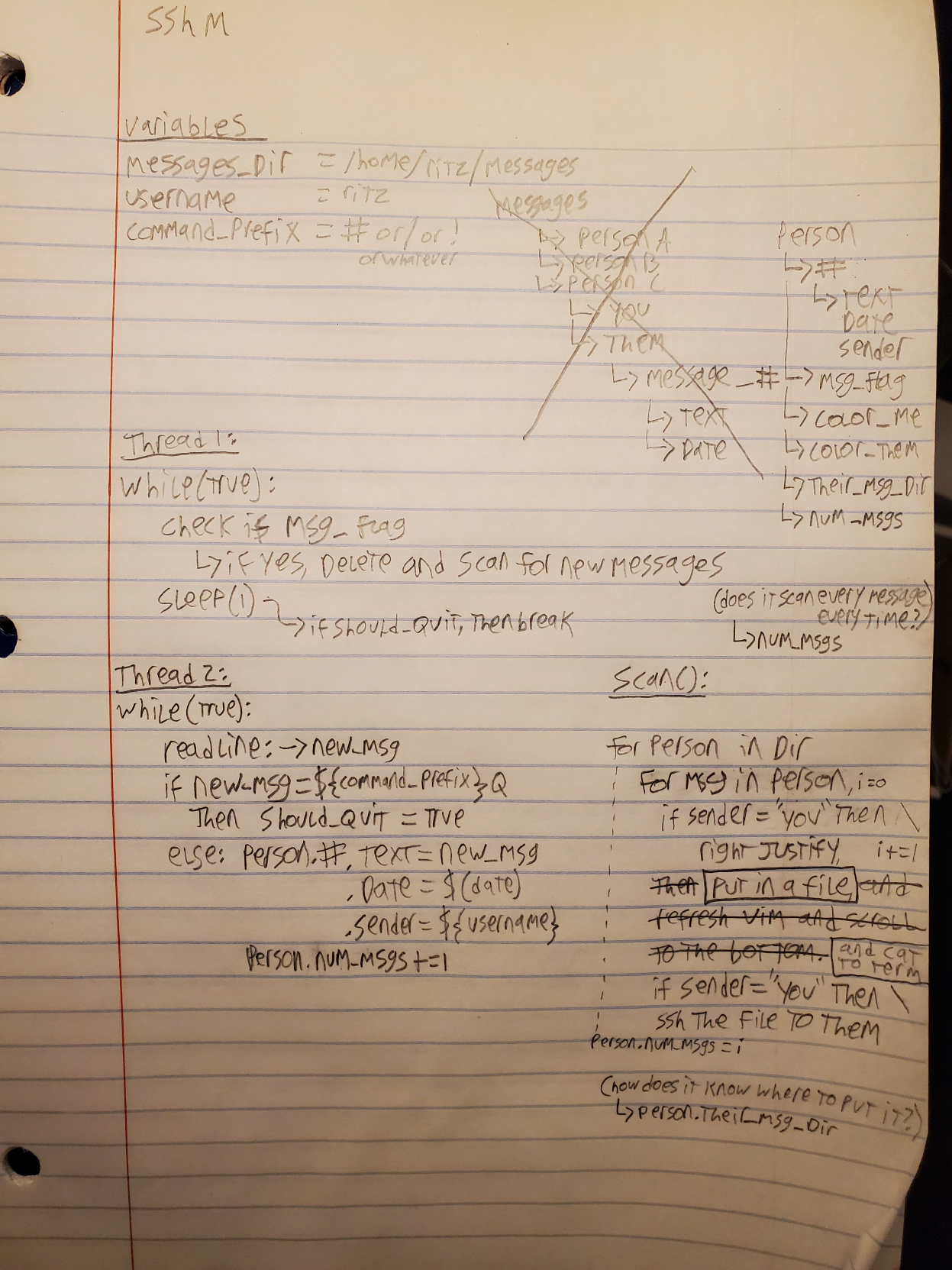
this is what I got so far for a messaging client that uses SSH
... so you need someone's public key in order to talk to them
┌─────────┐ ┌───────────┐
│ similar │ chronological │ different │
╘═════════╧╧════════════════════════════════════════════════════───────────────────────┘
|